BreakingPoint
“Real-world traffic and threat simulation to validate resilience, security, and performance.”
What is BreakingPoint?
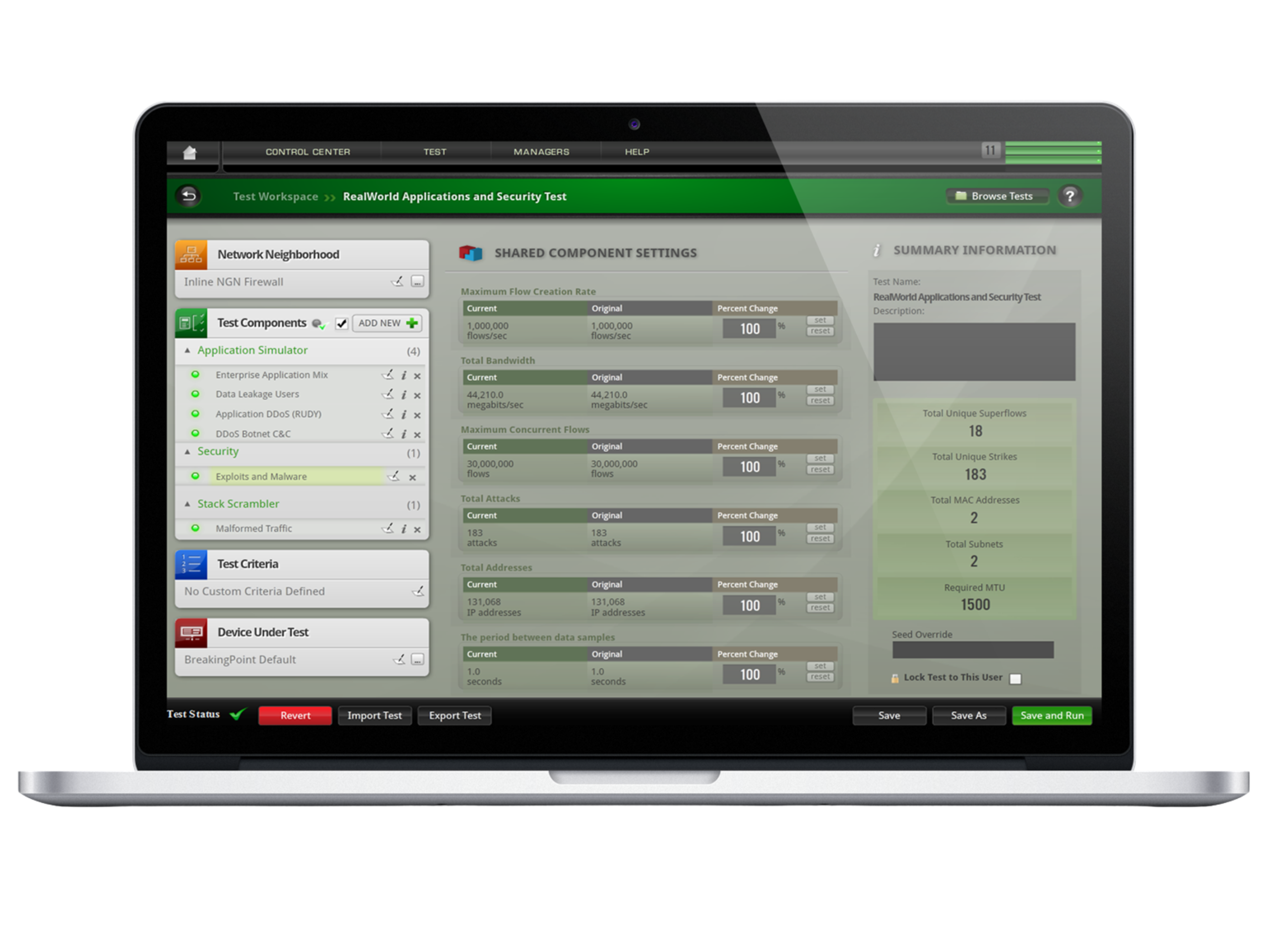
BreakingPoint is Keysight’s flagship security and resilience testing platform, combining hardware appliances and advanced software libraries to emulate real applications, users, and cyberattacks at massive scale.
It enables enterprises, governments, and service providers to validate the efficacy of firewalls, IPS, DDoS defenses, and industrial systems against today’s evolving threats — without jeopardizing production environments.
Key Features
- Hardware Platforms
- High-performance appliances capable of generating stateful traffic at hundreds of gigabits per second.
- Modular chassis options with scalable interface cards (1G to 100G, copper and fiber).
- Purpose-built for carrier-grade and national lab testing environments.
- Application and Traffic Simulation
- Emulates thousands of applications and protocols (HTTP, VoIP, video, SaaS, P2P).
- Generates realistic user behavior, at scale.
- Threat and Attack Simulation
- Continuously updated library of exploits, malware, ransomware, and evasion techniques.
- Emulates zero-day threats, advanced persistent threats (APT), and multi-vector attacks.
- Inline Security Validation
- Test firewalls, IPS, DDoS appliances, proxies, NDR, and industrial systems (SCADA/ICS).
- Validate inline device performance under safe, controlled test scenarios.
- Advanced Metrics & Analytics
- Real-time dashboards: throughput, latency, drops, error rates.
- Reports designed for compliance and executive visibility.
BreakingPoint Solves Your Real-World Test Challenges
- DDoS Protection – Simulate volumetric (network layer) and application-layer DDoS attacks to validate mitigation strategies.
- Zero-Day Readiness – Test resilience against unknown threats using continuously updated attack libraries.
- SCADA & Industrial Network Security – Assess vulnerabilities and resilience of OT and SCADA networks, critical for energy and utilities.
- Next-Gen Firewall / IPS Validation – Ensure inline security tools scale under real-world attack and traffic loads.
- Regulatory & Compliance Testing – Produce evidence of resilience for audits and certifications.
- Application Performance under Attack – Validate if critical business applications remain usable during cyber incidents.
Benefits for the Client
- Reduce risk proactively: identify weaknesses before attackers exploit them.
- Validate security investments: ensure firewalls, IPS, and DDoS appliances deliver promised performance.
- Operational confidence: test under realistic conditions, at scale.
- Critical infrastructure protection: extend testing to SCADA and industrial networks.
- Future-proof defense: continuous updates reflect the latest threats and attack trends.
Why BreakingPoint is Different ?
- Hardware-accelerated: dedicated appliances designed for massive scale and precision.
- Realism: combines real applications, real threats, and real user behavior.
- Continuously updated intelligence: always current with global threat landscape.
- Multi-domain coverage: enterprise IT, service provider backbones, and industrial OT/SCADA networks.
- Part of Keysight ecosystem: integrates with CyPerf, Vision Packet Brokers, and IxLoad.
Typical Use Cases
- Pre-deployment validation of next-gen firewalls and IPS.
- Benchmarking DDoS protection appliances.
- Securing critical infrastructure (SCADA, energy, utilities).
- Assessing cloud and hybrid network defenses.
- Running continuous security validation in labs and SOCs.
Services & Support (What We Offer)
- Security Test Assessment – determine BreakingPoint deployment scenarios.
- Lab Setup & Integration – deploy appliances and test libraries in enterprise/service provider labs.
- Workshops – DDoS simulation, SCADA resilience testing, zero-day readiness exercises.
- Managed Testing Services – continuous validation campaigns powered by BreakingPoint appliances.